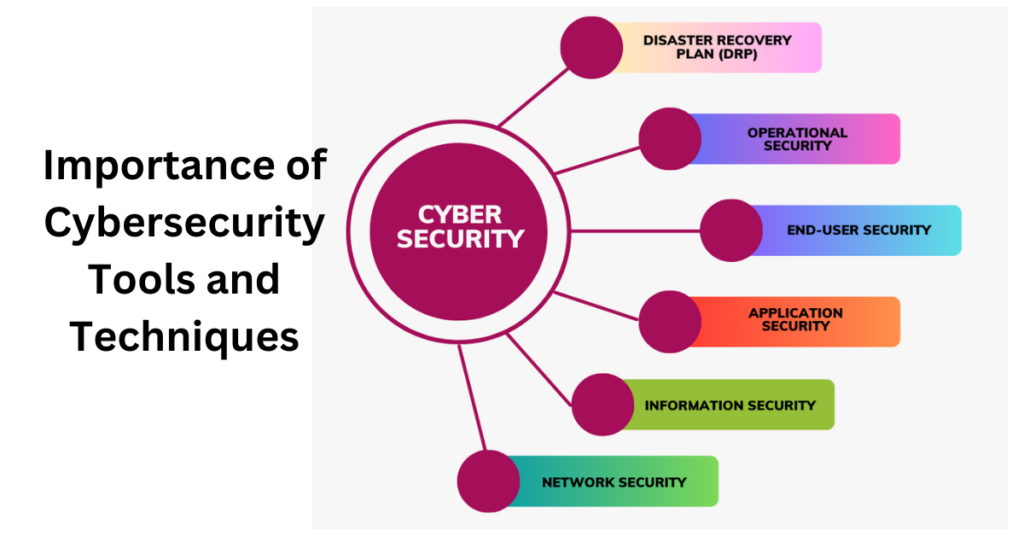
Cybersecurity tools and techniques are essential for protecting against cyber threats, safeguarding sensitive information, preventing financial losses, maintaining business continuity, building customer trust, complying with regulations, and ensuring national security. Investing in strong cybersecurity measures is crucial in today’s interconnected world where digital attacks are becoming more sophisticated and prevalent.
Cybersecurity tools and techniques play a crucial role in safeguarding digital systems, networks, and data from various cyber threats. Here are some reasons why they are essential:
- Protection Against Cyber Threats: Cybersecurity tools and techniques help protect individuals, organizations, and governments against various cyber threats such as malware, ransomware, phishing attacks, data breaches, and hacking attempts. These tools act as a line of defense, helping to detect, prevent, and respond to these threats effectively.
- Safeguarding Sensitive Data: Cybersecurity tools and techniques play a crucial role in safeguarding sensitive information such as personal data, financial records, intellectual property, and trade secrets. They help encrypt data, implement secure network protocols, and establish access controls, ensuring that confidential information remains protected from unauthorized access or disclosure.
- Preventing Financial Losses: Cyberattacks can lead to significant financial losses for individuals and businesses. Cybersecurity tools and techniques help minimize these losses by identifying and mitigating vulnerabilities in systems, detecting fraudulent activities, and preventing unauthorized access to financial accounts.
- Maintaining Business Continuity: A successful cyberattack can disrupt business operations and cause downtime, resulting in loss of productivity and revenue. Cybersecurity tools and techniques help ensure business continuity by effectively managing risks, implementing backup and recovery strategies, and reducing the impact of potential cyber standards that organizations must adhere to, such as the General Data Protection Regulation (GDPR) or the Payment Card Industry Data Security Standard (PCI DSS). Cybersecurity tools and techniques help organizations meet these requirements, ensuring legal and regulatory compliance.
- Safeguarding National Security: Cybersecurity is not just a concern for individual users and businesses; it is also vital for national security. Cybersecurity tools and techniques help protect critical infrastructure, such as power grids, transportation systems, and government networks, from cyber threats that could have severe consequences for a country’s economy, defense, and public safety.
Cyber security tools and techniques are used to protect computer systems, networks, and data from unauthorized access, attacks, and potential vulnerabilities. Some common cyber security tools and techniques include:
Firewalls: These act as a barrier between a trusted internal network and an untrusted external network, monitoring and controlling incoming and outgoing network traffic based on predetermined security rules.
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS): IDS and IPS tools monitor network traffic in real-time, detecting and preventing malicious activity and potential network intrusions.
Antivirus and Antimalware Software: These tools scan and detect malicious software (such as viruses, worms, Trojans) that can harm computer systems, and prevent them from executing or spreading.
Secure Socket Layer (SSL) Certificates and Transport Layer Security (TLS): SSL and TLS are encryption protocols used to establish secure communications over the internet. They ensure that data transferred between a web server and a client is encrypted and secure.
Vulnerability Scanners: These tools scan computer systems and networks to identify potential vulnerabilities, such as outdated software, misconfigurations, or weak passwords, which can be exploited by hackers.
Encryption: Encryption tools are used to convert sensitive information into an unreadable form (ciphertext) to protect it from unauthorized access. Only authorized parties with the decryption key can decipher the information.
Two-Factor Authentication (2FA) and Multi-Factor Authentication (MFA): These techniques require users to provide more than one form of authentication (such as a password and a verification code sent to a mobile device) to access a system or account, providing an extra layer of security.
Security Information and Event Management (SIEM): SIEM tools collect, analyze, and manage security event logs from various sources to identify and respond to security incidents in real time.
Penetration Testing: Also known as ethical hacking, penetration testing involves simulating real-world attacks to identify vulnerabilities and assess the security of computer systems, networks, and applications.
Security Awareness Training: Educating employees about good cyber security practices, such as recognizing phishing emails, avoiding suspicious links, and using strong passwords, is an essential technique to prevent human errors that can lead to security breaches.
Network Monitoring: Network monitoring tools are used to continuously monitor network traffic and detect any suspicious or malicious activity. This helps in identifying and mitigating potential threats and intrusions.
Data Loss Prevention (DLP): DLP tools help in monitoring and protecting sensitive data by identifying, classifying, and preventing unauthorized access, use, or transmission of data.
Patch Management: Regularly updating and applying patches to software, operating systems, and firmware is crucial to address known vulnerabilities and protect against potential cyber-attacks.
Endpoint Protection: Endpoint protection tools protect individual devices (such as desktops, laptops, and smartphones) from malware, unauthorized access, and data breaches.
Security Incident Response: Incident response tools and techniques involve analyzing, containing, and recovering from security incidents. This includes investigation, containment, eradication, and recovery processes to minimize the impact of a security breach.
It’s important to note that this is not an exhaustive list of all the tools and techniques used in cyber security, as the field is constantly evolving to address new threats and vulnerabilities. Additionally, the selection and implementation of these tools and techniques will vary depending on the specific needs and requirements of an organization or system.