XSS (Cross site scripting)
Cross-Site Scripting (XSS) attacks are a type of injection, in which malicious scripts are injected into otherwise benign and trusted websites. XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user. Flaws that allow these attacks to succeed are quite widespread and occur anywhere a web application uses input from a user within the output it generates without validating or encoding it.
TYPES
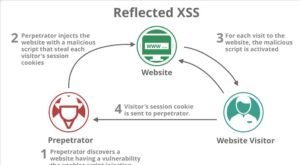
- Reflected:- Reflected XSS occurs when a script which entered by the client and its execute immediately and reflect result instantly.
- Stored:- Stored XSS occurs when a script executed and get permanently saved on the server and executed on every user pc who is using website.
- DOM Based:- DOM-based is most dangers XSS vulnerability because in this validations works fine but still script get executed somehow. in this case, the developer has to check every single line of code.
Working

Reflected(Working)
Stored (working)

XSS(DVWA)

- Since the main difference between reflected and stored is reflected execute script immediately and stored stores the script and execute every time.
- Now we are going to test scripts on DVWA on a different level.
- Here is a list of the script for testing XSS and bypass filters(validations).
XSS(DVWA)
- Open XSS reflected in DVWA and make sure security is set to low. Enter script:
- <script>alert(‘hi’)</script>
- The script gets executed immediate and reflects ‘hi’ in a popup dialog box
- This happens because there is no validation in the form field.
XSS(DVWA)
- Set security to medium. It will apply validation on the form field and execute the same code
- This happens because <script> is validated in coding but we can use it in the capital. I.E <script>
XSS(DVWA)
- Set security to high and again use the script.
- Here the whole word letter is validated but we can also use some other script. I.e <body BODY ONLOAD=alert(‘xss’)>
XSS(DVWA)
- Now go to security and set security to impossible and use the <svg> script tag.
- Here you can see a user token is used as validation so that every time its give a token and all the validation is used in the token generator function.