MOBILE FORENSICS: ATTACKS & SECURITY
Mobile Forensics:
Mobile forensics is a division of Digital Forensics that deals with mobile phones and other mobile devices.
Or we can say Mobile Forensics is a division of computer forensics handles cases of recovering evidence from mobile and other related devices under the forensically sound condition.
Now a day’s with increasing the usage of mobile phones, crimes related to mobile devices growing continuously.
Mobile Forensics division handle cases not only related to mobile phones but also Tablets, Digital Cameras, SD Cards, SIM Cards, and PDA (Personal digital assistant), etc.
WHY MOBILE FORENSICS?
Mobile forensics aims to trace the perpetrators or criminals of crimes that involve the use of mobile phones, SIM cards and other mobile related devices to commit a crime.
Now a day’s mobile phones are being one of the most reliable evidence involves almost every crime. Mobile phones are used to LINK TO REGULAR CRIMES (Credit/Debit Cards Fraud, Pornography, Human Trafficking, Drug supply, etc.)
Now with increasing Information Technology, the use of smartphones increased and due to digitalization, the trend of Mobile Payment increased in recent years. But with increasing the Technology the no of mobile threats also increased, Resulting in the Increase in Importance of Mobile Forensics to Solve a Crime.
MOBILE DEVICES TARGETING THREATS
As the growth of the IT Sector increasing, the no of security threats increasing day by day.
The majority of the population is not aware of the potential of – Smartphones, PDA devices (Personal digital assistant), Cameras, iPods and the risks related to their destructive use. The Mobile device Forensics or we can say Forensics of Mobile Devices is primarily performing on mobile phones, SIM Cards, and PDA devices; now it also involves digital cameras, Tablets, etc. Now we are going to discuss Mobile and other related Devices Threats.
The following are the different types of threats targeting mobile devices:
- Social Engineering Attacks
- Malware
- Network & Web Attacks
- Data Loss
- Data Integrity
1. Social Engineering Attacks
Social Engineering Attacks are one of the most common and popular attacks for mobile devices. The criminal or hacker/attacker, attract or we can say entice the victim (target) to share his/her personal information, for example, sensitive information, personal & professional details, bank statement, social media credentials, credit or debit card no and pin and OTP no.
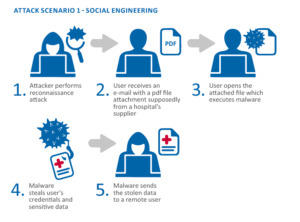 Some common Social Engineering Attacks are given below:
Some common Social Engineering Attacks are given below:
- Phishing Attacks
- Pretexting
- Tailgating
- Baiting
2. Network & Web Attacks

Now a day’s web attacks and network-based attacks are common security threats for mobile devices. Criminal or the attacker commonly attacks through malicious web-pages or websites.
In Web-based attacks criminal commonly send a malicious link through any medium which redirects the victim to a specific web page containing suspicious activities.
And in case of networks attacks criminal or attacker attack through the system, attacker hacks the networking area, or we can say Wi-Fi of the victim and try to commit illegal activity through that without the knowledge of the user.
3. Malware Attacks
The attacker or criminal install or try to install malware to commit the crime. And after malware installation criminal steals confidential data and other personal information for his/her own use without the knowledge of the victim
Types of malware:
- Virus
- Worms
- Spywares
- Keyloggers
- Trojan Horse
4. Data Loss and Misuse
The misuse of useful and confidential data is the most common. Criminal steal personal/sensitive data of the victim and abuse that information for revenge or to spoil the social value of the victim.
The loss and transfer of data may be due to the unauthorized remote access to the device or may be due to induced unintentionally by a legitimate mobile user.
5. Data Integrity Threats

Data Integrity Threats are the threats to mobile devices that corrupt the data or attempt to modify the data stored in the mobile and related methods.
These types of attacks are aimed for financial gain or for disturbing the normal mental or physical functionally. Attackers and criminal also spread such kind of threads to destroy the business of the victim for revenge.
Some More Interesting Pieces of Stuff For You
Latest Blog
A BEGINNERS GUIDE TO CYBERSECURITY TRAINING, CERTIFICATION AND JOBS
If that’s the case, feel free to visit these helpful links
♦ How to become a Hacker After 12th?
♦ How to Start your Career in Hacking?
♦ Future of Ethical Hacking & Cyber Security In India?
♦ What kinds of jobs are there in Cyber Security?
♦ Types of jobs for an Ethical Hacker?








